
What does the Capitol riot mean for US cybersecurity?
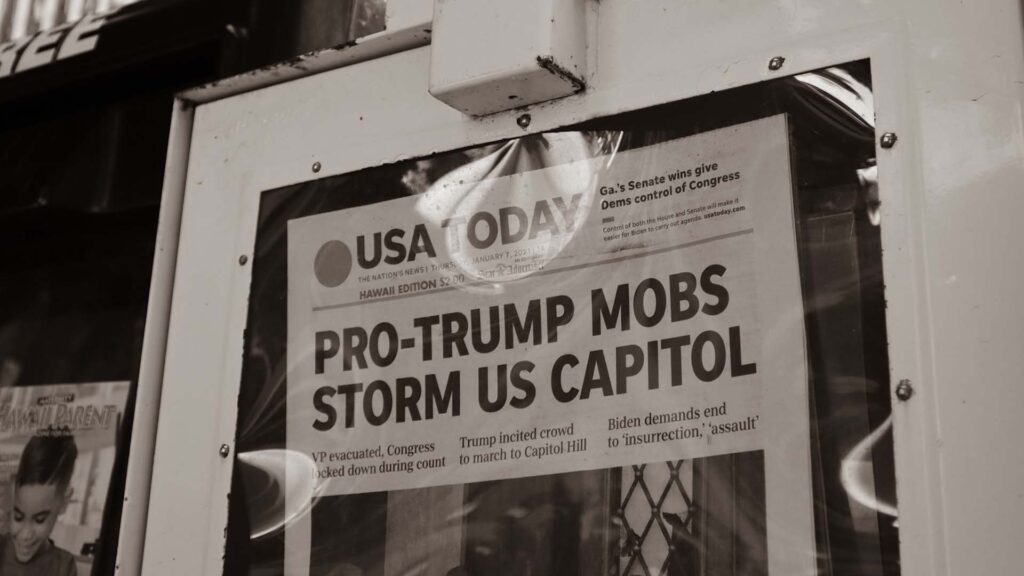
January 6th: what should have been a momentous day for Joe Biden and Kamala Harris will be etched in history for the Capitol Hill riot. 5 died including a police officer and 100s of injuries occurred including 56 officers. Utter tragedy.
What has grabbed fewer headlines is the damage sustained to cybersecurity and the possibility the digital Capitol Hill could still be at risk.
What has the digital impact of the Capitol Riots been?

Richard Barnett, the man pictured with his feet atop Nancy Pelosi’s desk, remains under house arrest with no internet access permitted. He, and other insurrectionists, are the investigative focus of a Stage IV hack at Capitol Hill. Stage IV refers to a cyber assault where hackers had administrative control of the network with the ability to create accounts, plant hard and software bugs, and steal information.
Such vociferous claims are not without merit as rioters were granted 4 hours of unrestricted access to internal documents, networks, intel, email records, and private conversations. In addition, the laptop of Senator Jeff Merkley was snatched.
Undoubtedly, the mindset of the attackers is questionable at best. However, to assume there was no planning, digital sophistication or any domestic or foreign bad actors is more than naïve.
What happens next for US Cybersecurity?
Worst case scenario must be assumed. There is a possibility that every digitally connected device to the Capitol system was exposed and under the control of domestic terrorists. The threat is unprecedented and rightfully claimed resignations of Paul Irving and Michael Stenger, House and Senate Sergeants-at-arms, and the Chief of Capitol Police, Steven Sund.
Step 1: Secure Networks
The cleanup operation will be incredibly challenging. The first-level sweep of hardware planted has already occurred meaning any physical recording devices will be found. An equivalent digital search has also taken place. Sensitive compartmented information was not breached meaning the level above top secret remains safe on an alternate network.
A social media sweep will be required for years to come as the potential for materials to be shared is uncontrollable.
Step 2: Track Perpetrators Down
With rioters being arrested each day, finding those responsible for cyber breaches will be a challenge within a challenge. Biometric information, facial recognition from Clearview AI, social scanning, internal cameras, fingerprinting and many more are the tools at the disposal of those involved in the hunt. Even then, attackers will remain elusive.
Step 3: Charge Rioters, Ringleaders, and Inciters
Trump is, unquestionably, the origin of these attacks but remains unlikely to face prosecution under privacy suits. His followers, demanding pardons, are unlikely to be so fortunate. When those responsible for the cybersecurity attack are brought to justice, they will face federal charges under the following acts:
- Espionage Act 1917 (Formerly Sedition Act 1798 & 1918)
- Computer Fraud and Abuse Act
- Electronic Communications Privacy Act 1986
- Wiretap Act
- Stored Communications Act
- Trap and Trace Devices Statute
Rioters will be charged criminally and civilly where breaches are proven and depending on the depth and what occurred with the data, historic sentences may be handed down.
Step 4: Review Cybersecurity Protocols
Cybersecurity at Capitol Hill is of the highest standard in the world. Like most systems, however, human error is still a factor in 95% of breaches. As witnessed in the Hillary Clinton E-mails scandal, nobody is immune.
The likely outcome is a more rigorous assessment of individual security behavior. With data storage, decision making and working from different offices factored in, an education-based approach is on the horizon. From a hard and software perspective, Capitol Hill IT Security will continue to invest in the most bulletproof systems available.
In Conclusion…
The Capitol Hill riots were the most harrowing, domestic-led attack on US democracy in living memory. Loss of life, injury, and legal recourse will capture headlines, but the digital exposure may be felt for years to come.
The ill-witted insurrectionists fail to realize the vehicle they created for cyber-attackers. They potentially gifted foreign intelligence bad actors untethered access to the highest offices below presidency. Ironically, this is a fear of most of these extremists.
As America watches, the corridors of cybersecurity feverishly try to uncover the extent of the damage and restore security during the darkest of times. For those responsible, the full force of law will account for their misadventure.