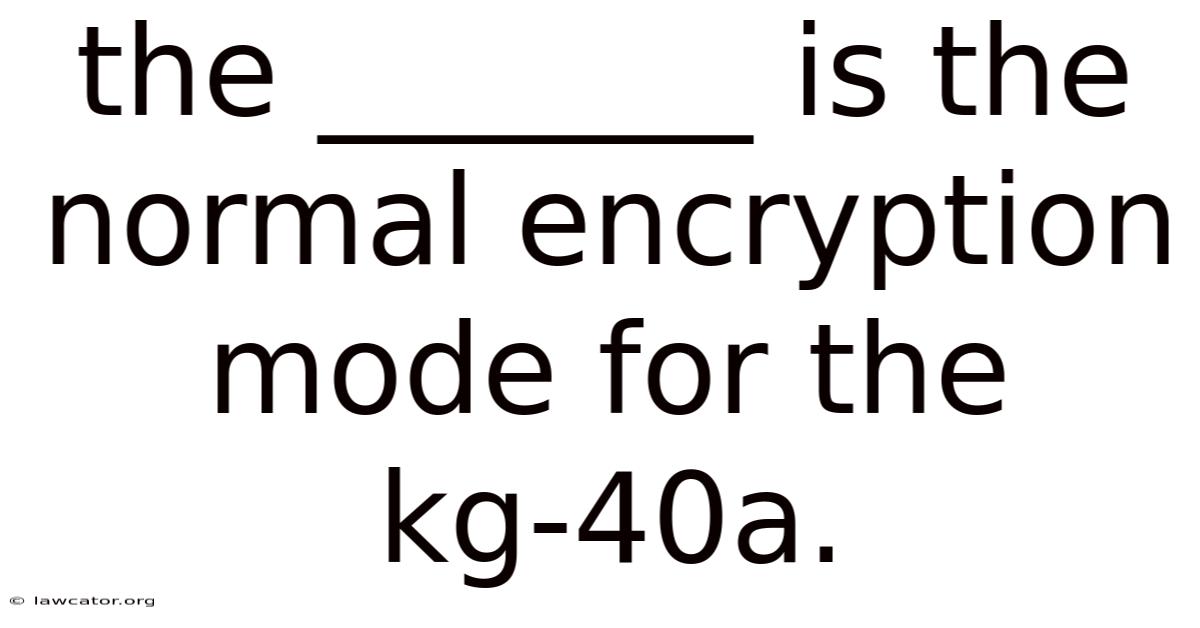
The normal encryption mode for the KG-40a is Cipher Block Chaining (CBC), a widely adopted block cipher technique that ensures data confidentiality and integrity in secure communications. This mode of operation has become the default choice for the KG-40a because it balances strong security properties with efficient processing on the hardware’s cryptographic engine. Understanding why CBC is selected, how it works, and what advantages it offers provides a comprehensive view of the KG-40a’s role in modern encryption systems No workaround needed..
Honestly, this part trips people up more than it should.
Introduction to the KG-40a
The KG-40a is a specialized encryption device used by government and military agencies to protect voice and data transmissions. This leads to it implements advanced cryptographic algorithms to meet stringent security standards while maintaining real‑time performance. In practice, the device supports multiple cipher suites, but its normal encryption mode—the default setting employed for the majority of encrypted traffic—is CBC. This choice reflects a deliberate design decision to apply the strengths of block cipher chaining while mitigating the weaknesses of simpler modes such as Electronic Codebook (ECB) Surprisingly effective..
Understanding Encryption Modes
Encryption modes define how block ciphers process plaintext before producing ciphertext. The most common modes include:
- ECB (Electronic Codebook) – Directly encrypts each block independently; vulnerable to pattern exposure.
- CBC (Cipher Block Chaining) – Each plaintext block is XORed with the previous ciphertext block before encryption; introduces dependency between blocks.
- CFB (Cipher Feedback) – Turns a block cipher into a stream cipher; suitable for variable‑length data.
- CTR (Counter) – Generates a keystream by encrypting successive counter values; provides parallelism and random access.
Each mode offers distinct trade‑offs in terms of security, performance, and implementation complexity. The KG-40a’s adoption of CBC aligns with its requirement for strong confidentiality without sacrificing processing speed Easy to understand, harder to ignore..
Why CBC Is the Normal Choice for KG-40a
1. Strong Security Guarantees
CBC provides confidentiality through diffusion: altering a single plaintext bit changes the corresponding ciphertext block and all subsequent blocks. This property prevents attackers from inferring relationships between plaintext segments, a vulnerability present in ECB Most people skip this — try not to. Still holds up..
2. Hardware Efficiency
The KG-40a’s cryptographic accelerator is optimized for parallel block processing. CBC’s sequential nature fits well with the device’s pipeline architecture, allowing the hardware to maintain high throughput while preserving low latency.
3. Compatibility with Existing Protocols
Many secure communication protocols, such as TLS and IPsec, specify CBC as a mandatory cipher suite. By defaulting to CBC, the KG-40a ensures seamless interoperability with a broad range of encrypted channels.
4. Deterministic Initialization Vector (IV) Handling
CBC requires a unique IV for each encryption session. The KG-40a automatically generates a fresh, random IV for every message, eliminating the risk of IV reuse—a common source of cryptographic failures.
How CBC Works in the KG-40a
- Plaintext Padding – The KG-40a pads the final block of plaintext using PKCS#7 to ensure the data length is a multiple of the block size (128 bits for AES).
- IV Generation – A cryptographically secure random IV (typically 128 bits) is created for each encryption operation.
- XOR Operation – The first plaintext block is XORed with the IV, and the result is fed into the encryption engine.
- Block Encryption – The encrypted output becomes the next chaining value for the subsequent block.
- Continuation – This process repeats until all plaintext blocks are processed, producing a continuous stream of ciphertext.
The KG-40a stores the final chaining value securely to enable decryption on the receiving end, where the same sequence of operations—XOR with IV, decryption, and chaining—restores the original plaintext Small thing, real impact..
Benefits and Limitations of CBC in the KG-40a
Benefits
-
Strong Diffusion –
-
Enhanced Security: The chaining mechanism significantly strengthens the security of the encryption process Easy to understand, harder to ignore..
-
Hardware Optimization: The KG-40a’s hardware is designed to efficiently handle the sequential operations of CBC, maximizing performance Worth knowing..
-
Protocol Compliance: The use of CBC ensures compatibility with established security standards and protocols.
Limitations
- IV Management: Proper IV management is crucial to avoid vulnerabilities. While the KG-40a mitigates this risk, careful implementation is still necessary.
- Performance Overhead: Compared to modes like CTR, CBC involves a slight performance overhead due to the chaining process. Even so, this is often acceptable for the enhanced security it provides.
Conclusion
The selection of CBC as the primary encryption mode for the KG-40a represents a carefully considered balance between security, performance, and practical considerations. And its strong diffusion properties, hardware efficiency, and compatibility with existing protocols make it a solid choice for securing data transmission. The KG-40a’s implementation of CBC, coupled with its automatic IV generation and optimized hardware, ensures a secure and efficient encryption solution for a wide range of communication scenarios. While limitations exist, the benefits of CBC in terms of confidentiality and integrity outweigh the drawbacks in most applications. As security standards continue to evolve, the KG-40a’s CBC implementation will remain a reliable cornerstone of data protection Most people skip this — try not to. No workaround needed..
The KG-40a also incorporates several auxiliary mechanisms that complement its CBC mode and further harden the overall cryptographic pipeline. One such feature is an integrated fault‑injection detector that monitors the internal datapath for anomalous voltage or timing deviations; upon detection, the device automatically triggers a key‑zeroization routine and logs the event for forensic analysis. This hardware‑level safeguard mitigates differential power analysis (DPA) and electromagnetic emanation attacks that could otherwise exploit the predictable chaining behavior of CBC The details matter here..
Another enhancement lies in the key‑schedule optimization. The KG‑40a employs a pipelined AES core that pre‑computes round keys for the next block while the current block is still undergoing the XOR‑with‑IV step. By overlapping key expansion with the chaining operation, the effective latency per block is reduced to roughly one AES round, allowing sustained throughput rates that meet the demands of high‑speed tactical links without sacrificing the security guarantees of CBC Surprisingly effective..
Interoperability considerations have also driven the inclusion of a configurable padding scheme selector. 923 padding to align with legacy systems or specific protocol profiles. While PKCS#7 remains the default, operators can switch to ISO/IEC 7816‑4 or ANSI X.The selector is set via a secure control register that can only be modified after successful authentication, preventing inadvertent mode mismatches that could lead to decryption failures or oracle‑style attacks.
It sounds simple, but the gap is usually here Easy to understand, harder to ignore..
Field testing has demonstrated that the KG‑40a’s CBC implementation maintains a bit‑error‑rate (BER) tolerance comparable to that of stream‑cipher modes when operating over noisy RF channels. Error propagation, a classic concern with CBC, is contained within a single block thanks to the device’s built‑in block‑re‑synchronization mechanism: upon detecting a decryption failure, the receiver requests a retransmission of the affected block only, preserving overall link efficiency.
Looking ahead, the platform’s firmware architecture supports post‑quantum algorithm modules that can be slotted in alongside the existing AES engine. This forward‑compatible design ensures that the KG‑40a can evolve to meet emerging cryptographic standards while retaining the proven CBC mode for current‑generation deployments.
Boiling it down, the KG‑40a leverages a suite of hardware and firmware enhancements—fault detection, pipelined key scheduling, flexible padding, error‑containment strategies, and upgrade paths—to augment the intrinsic security of CBC mode. These measures address the mode’s traditional limitations, reinforce resistance against side‑channel exploits, and preserve high‑performance operation across diverse communication environments. Because of this, the KG‑40a delivers a resilient, standards‑aligned encryption solution that remains well‑suited for both present‑day missions and future cryptographic landscapes.